
最近、私は幸運にも、国際的な企業であるCoffeeupのパブリックインターネットアクセスを整理するという、かなり興味深い実用的なタスクに取り組むことができました。», 5 « » , . , : . , , , : . , , , . « », . , 3700 . .
, . , , «» , , , 1000 . «Coffee up» 5000 /, 60 000 / ( ). - – , . , . .
:
- , .
.
.
Hotspot ( ).
( , , backend frontend).
-
. 31 2014 . №758 « …» 12 2014 . №801 « …». , , 2 . ( ):
, , .
, (, ..). :
…, … 6 .
« » , . : «NetFlow» ( , https://en.wikipedia.org/wiki/NetFlow).
, . 27 2006 . №152- « ». , , – : , , .. Hotspot ? … – . (https://15.rkn.gov.ru/p8880/p15987/):
. 3 27.07.2006 №152- « »
- , ( ). ( ) , ( ) . , , ( ) .
. MikroTik : Hotspot, , , . , 2.4 5 , WiFi . «hAP ac lite TC» ( https://mikrotik.com/product/RB952Ui-5ac2nD-TC, , «Operating System RouterOS»). 3700 , . – , , , . Linux , - .
. -, - 4G USB , - WiFi . - , - , – . MikroTik . , WiFi ( 4G USB ):
/interface wireless security-profiles set [ find default=yes ] supplicant-identity=MikroTik
add authentication-types=wpa2-psk disable-pmkid=yes eap-methods="" group-ciphers=tkip mode=dynamic-keys name=OPERATOR supplicant-identity="" unicast-ciphers=tkip wpa2-pre-shared-key=1111111111111
/interface wireless set [ find default-name=wlan1 ] band=2ghz-onlyn country=russia disabled=no frequency=auto name=wlan1-station security-profile=OPERATOR ssid=OPERATOR-9392 station-roaming=enabled
dhcp-client NAT ( masquerade, MikroTik «My holy war against masquerade», , masquerade SRC-NAT ):
/ip firewall nat
add action=src-nat chain=srcnat comment=OPERATOR-NAT out-interface=wlan1-station src-address=192.168.2.0/24 to-addresses=10.0.0.100
add action=src-nat chain=srcnat comment=HOME-NAT out-interface=wlan1-station src-address=192.168.1.0/24 to-addresses=10.0.0.100
/ip dhcp-client
add disabled=no interface=wlan1-station use-peer-dns=no use-peer-ntp=no
#Script for src-NAT
:local OUTINTERFACE wlan1-station;
:local COMMENT OPERATOR-NAT;
:local COMMENT2 Home-NAT;
:local IPFORNAT [/ip dhcp-client get [find interface=$OUTINTERFACE] address];
#delete mask in ip
:local IPFORNATSHORT [:pick $IPFORNAT 0 [:find $IPFORNAT "/"]];
/ip firewall nat set [find comment=$COMMENT] to-addresses=$IPFORNATSHORT;
/ip firewall nat set [find comment=$COMMENT2] to-addresses=$IPFORNATSHORT;
MikroTik- , . . WiFi (free staff), 3 WiFi : staff ( 2.4 5 , 5 ) free ( 5 ). 2.4 free , , 4 . staff, , , "" . WiFi -, . , , WiFi ( ), master.
/interface wireless security-profiles
set [ find default=yes ] supplicant-identity=MikroTik
add authentication-types=wpa-psk,wpa2-psk eap-methods="" management-protection=allowed name=coffeecup_free supplicant-identity=""
add authentication-types=wpa2-psk disable-pmkid=yes eap-methods="" management-protection=allowed mode=dynamic-keys name=coffeecup_staff supplicant-identity="" wpa2-pre-shared-key=2222222222222
/interface wireless
set [ find default-name=wlan1 ] antenna-gain=0 band=2ghz-g/n channel-width=20/40mhz-XX country=russia disabled=no frequency=auto frequency-mode=manual-txpower installation=indoor mode=ap-bridge name=wlan1-COFFEECUP_2_staff security-profile=coffeecup_staff ssid=CoffeeCup_Staff2 station-roaming=enabled wireless-protocol=802.11 wps-mode=disabled
set [ find default-name=wlan2 ] antenna-gain=0 band=5ghz-n/ac channel-width=20/40/80mhz-XXXX country=russia disabled=no frequency=auto frequency-mode=manual-txpower installation=indoor mode=ap-bridge name=wlan2-COFFEECUP_5_staff security-profile=coffeecup_staff ssid=CoffeeCup_Staff station-roaming=enabled wps-mode=disabled
add default-forwarding=no disabled=no keepalive-frames=disabled mac-address=02:00:00:AA:00:00 master-interface=wlan2-COFFEECUP_5_staff multicast-buffering=disabled name=wlan3-COFFEECUP_5 security-profile=coffeecup_free ssid=CoffeeCup_FreeWiFi wds-cost-range=0 wds-default-cost=0 wps-mode=disabled
firewall, icmp ( ) VPN. 4G :
/ip firewall filter
add action=accept chain=input comment="Accept established,related" connection-state=established,related
add action=drop chain=input comment="Drop invalid" connection-state=invalid
add action=accept chain=input comment="Accept input icmp" protocol=icmp
add action=accept chain=input comment="Accept input ovpn" in-interface=ovpn-coffeecup
add action=accept chain=input comment="Accept input DNS for bridge_guest" dst-port=53 in-interface=bridge_guest protocol=udp
add action=drop chain=input comment="Drop all input from !bridge" in-interface=!bridge
add action=accept chain=forward comment="Accept established,related" connection-state=established,related
add action=drop chain=forward comment="Drop invalid" connection-state=invalid
add action=drop chain=forward comment="Drop all from WAN to !DSTNAT" connection-nat-state=!dstnat connection-state=new in-interface=LTE1_WAN
/ip firewall mangle
add action=mark-connection chain=prerouting comment="Managment connections" dst-address=192.168.15.21 dst-port=22,8291 new-connection-mark="Managment connections" passthrough=yes protocol=tcp
add action=mark-connection chain=forward comment="VIP connection" connection-mark=no-mark new-connection-mark="VIP connection" passthrough=yes src-address-list=VIP
add action=mark-packet chain=forward comment="VIP packets" connection-mark="VIP connection" new-packet-mark="VIP packets" passthrough=yes
add action=mark-connection chain=forward comment="LAN=>WAN connections" connection-mark=no-mark in-interface=bridge new-connection-mark="LAN=>WAN connections" out-interface=LTE1_WAN passthrough=yes
add action=mark-packet chain=forward comment="LAN=>WAN packets" connection-mark="LAN=>WAN connections" new-packet-mark="LAN=>WAN packets" passthrough=yes
add action=mark-connection chain=forward comment="Guest=>WAN connections" connection-mark=no-mark in-interface=bridge_guest new-connection-mark="Guest=>WAN connections" out-interface=LTE1_WAN passthrough=yes
add action=mark-packet chain=forward comment="Guest=>WAN packets" connection-mark="Guest=>WAN connections" new-packet-mark="Guest=>WAN packets" passthrough=yes
add action=mark-packet chain=output comment="Managment packets" connection-mark="Managment connections" new-packet-mark="Managment packets" passthrough=yes
add action=mark-connection chain=postrouting comment="OVPN connections" dst-address=IP_OUR_SERVER dst-port=1190 new-connection-mark="OVPN connections" out-interface=LTE1_WAN passthrough=yes protocol=tcp
add action=mark-packet chain=postrouting comment="OVPN packets" connection-mark="OVPN connections" new-packet-mark="OVPN packets" passthrough=yes
/queue tree
add comment="Guest (bridge-guest)" max-limit=10M name=Guest parent=bridge_guest
add comment="LAN (bridge)" max-limit=10M name=LAN parent=bridge
add comment="WAN (pppoe)" max-limit=10M name=WAN parent=LTE1_WAN
add name=Guest_other packet-mark=no-mark parent=Guest
add name="LAN_LAN=>WAN" packet-mark="LAN=>WAN packets" parent=LAN
add limit-at=128k max-limit=512k name=LAN_managment packet-mark="Managment packets" parent=LAN priority=1
add name=LAN_other packet-mark=no-mark parent=LAN
add name=LAN_ovpn packet-mark="OVPN packets" parent=LAN
add name=LAN_vip packet-mark="VIP packets" parent=LAN priority=7
add name="WAN_Guest=>WAN" packet-mark="Guest=>WAN packets" parent=WAN
add name="WAN_LAN=>WAN" packet-mark="LAN=>WAN packets" parent=WAN priority=7
add name=WAN_ovpn packet-mark="OVPN packets" parent=WAN priority=7
add name=WAN_vip packet-mark="VIP packets" parent=WAN priority=6
add name="Guest=>WAN" packet-mark="Guest=>WAN packets" parent=Guest queue=pcq-download-default
DNS : - , .
/ip dns set allow-remote-requests=yes servers=77.88.8.7,77.88.8.3
, DNS-. , DNS DHCP- ( use-peer-ntp) DNS VPN , NAT ip forward:
# :
/ip route
add distance=1 dst-address=77.88.8.3/32 gateway=192.168.15.1
add distance=1 dst-address=77.88.8.7/32 gateway=192.168.15.1
# :
iptables -t nat -A POSTROUTING -s 192.168.15.0/24 -o eth0 -j SNAT --to your_server_ip
echo '1' > /proc/sys/net/ipv4/ip_forward
Hotspot
Hotspot . MikroTik , "Coffee Cup", . (https://mikrotik-training.ru/), MikroTik, . . Hotspot. free web Hotspot coffeecuptogo.com, «cookie» 4 ( ). Hotspot, , .
/ip hotspot profile
set [ find default=yes ] dns-name=coffeecuptogo.com hotspot-address=192.168.10.1 html-directory=flash/hotspot http-cookie-lifetime=4h name=coffeecup
/ip hotspot
add address-pool=pool_guest addresses-per-mac=1 disabled=no idle-timeout=none interface=bridge_guest name=hotspot_coffeecup
/ip hotspot user profile
set [ find default=yes ] keepalive-timeout=1h mac-cookie-timeout=4h
, . . , http-get , ( ). , , , . : ( ), ( , , backend- ), mac , ip , ip ( , $_SERVER PHP, backend), , Hotspot ( 7), ( - ). iOS , . LOGIN (LOGIN=2) (LOGIN=1). :
#Out interface to internet
:local INTERNETINTERFACE pppoe-out1;
:local APIKEY 12345;
#status ---> log in
:local LOGIN 1;
:local SITE oursite;
:local PORT 1500;
:local nas [/system identity get name];
:local today [/system clock get date];
:local time1 [/system clock get time ];
:local ipuser [/ip hotspot active get [find user=$user] address];
:local usermac [/ip hotspot active get [find user=$user] mac-address]
:local hour [:pick $time1 0 2];
:local min [:pick $time1 3 5];
:local sec [:pick $time1 6 8];
:set $time1 [:put ({hour} . {min} . {sec})]
:local mac1 [:pick $usermac 0 2];
:local mac2 [:pick $usermac 3 5];
:local mac3 [:pick $usermac 6 8];
:local mac4 [:pick $usermac 9 11];
:local mac5 [:pick $usermac 12 14];
:local mac6 [:pick $usermac 15 17];
:local USERLONG "7$user";
:set $usermac [:put ({mac1} . {mac2} . {mac3} . {mac4} . {mac5} . {mac6})]
#ip addresses:
:local whiteip ([/tool fetch url="https://site_for_white_ip/" output=user as-value]->"data");
:local grayip [/ip address get [find interface=$INTERNETINTERFACE] address];
#delete mask in ip
:local grayipshort [:pick $grayip 0 [:find $grayip "/"]];
#What host-name
:foreach i in=[/ip dhcp-server lease print as-value where address=$ipuser] do={
:if (($i->"address")=$ipuser) do={
:set $host [($i->"host-name")];
}
}
do {/tool fetch url="https://$SITE:$PORT/\?api=$APIKEY&device=$nas\
&tel=$USERLONG\
&status=$LOGIN\
&ipgray=$grayipshort\
&ipnat=$ipuser\
&mac=$usermac\
&date=$today\
&time=$time1\
&host=$host"\
keep-result=no} on-error={};
:
#Out interface to internet
:local INTERNETINTERFACE pppoe-out1;
:local APIKEY 12345;
#status ---> log out
:local LOGIN 2;
:local SITE oursite;
:local PORT 1500;
:local nas [/system identity get name];
:local today [/system clock get date];
:local time1 [/system clock get time ];
:local hour [:pick $time1 0 2];
:local min [:pick $time1 3 5];
:local sec [:pick $time1 6 8];
:set $time1 [:put ({hour} . {min} . {sec})]
:local USERLONG "7$user";
#ip addresses:
:local whiteip ([/tool fetch url="https://site_for_white_ip/" output=user as-value]->"data");
:local grayip [/ip address get [find interface=$INTERNETINTERFACE] address];
#delete mask in ip
:local grayipshort [:pick $grayip 0 [:find $grayip "/"]];
do {/tool fetch url="https://$SITE:$PORT/\?api=$APIKEY&device=$nas\
&tel=$USERLONG\
&status=$LOGIN\
&ipgray=$grayipshort\
&date=$today\
&time=$time1"\
keep-result=no} on-error={};
, , , , Hotspot. , , 10 ( scheduler, ). :
/system logging add action=hotspot topics=hotspot,debug,info,!account
/system logging action add name=hotspot target=memory
MikroTik «hotspot» «login failed». . : Hotspot, , , 10 SMS, . -: Hotspot ( «login failed»), ( ) http-get backend ( , ), Hotspot, http-get SMS ( ) «» «hotspot» ( 1 1000 ). , RouterOS , ( ..) . MikroTik . , SMS ( SMS ). firewall, . Hotspot ( ) /ip firewall address-list 5 , Hotspot, , . «» address-list – RouterOS IP DNS . . SMS sms.ru, , caller id «Coffee Cup» ( , SMS).
:local SITE oursite;
:local PORT 1500;
:foreach line in=[/log find buffer=hotspot message~"login failed"] do={
:do {:local content [/log get $line message];
:local pos1 [:find $content " (" 0];
:if ($pos1 != " ") do={
:local uname "";
:set uname [:pick $content ($pos1-10) ($pos1-0)];
:local unameforsms "7$uname";
#Cheks user from spam
:local sendtest yes;
:foreach i in=[/ip firewall address-list print as-value where list=spam_cheks_list] do={
:if (($i->"address")=$uname) do={
:set $sendtest no;
}
}
:if ($sendtest=yes) do={
/ip firewall address-list add list=spam_cheks_list address=$uname timeout=00:05:00;
#Password generation
local pass ([/tool fetch url="https://$SITE:$PORT" output=user as-value]->"data")
#Add hotspot user
do {/ip hotspot user add name=$uname} on-error={};
do {/ip hotspot user set password=$pass numbers=[find name=$uname]} on-error={};
#SMS
do {/tool fetch url="https://sms.ru/sys/send.php\?AUTH_DATA&phones=$unameforsms&mes=$pass" keep-result=no} on-error={};
:delay 1;
}
}
}
}
#Clear hostpot log
/system logging action set hotspot memory-lines=1;
:delay 1;
/system logging action set hotspot memory-lines=1000;
, «Net-flow». backend-:
apt install flow-tools
nano /etc/flow-tools/flow-capture.conf
#comment all
#IMPORTANT Traffic Flow Version need 5 !!
-w /var/log/flow -n 275 -N 3 192.168.15.1/0/1234
MikroTik ( 5 , ):
/ip traffic-flow set enabled=yes interfaces=bridge_guest
/ip traffic-flow target add dst-address=192.168.15.1 port=1234 version=5
( ) «Net-flow» VPN ( ). . Hotspot RouterOS , . /flash/hotspot/login.html /flash/hotspot/alogin.html. – , – , . https://wiki.mikrotik.com/wiki/Manual:Customizing_Hotspot.
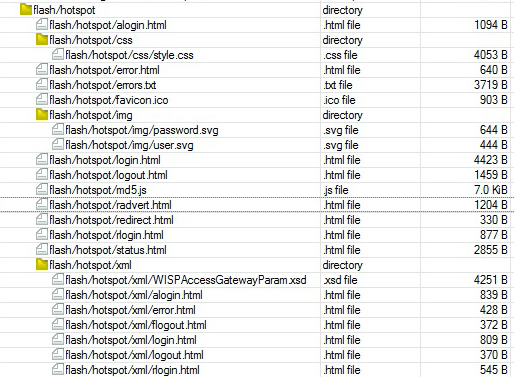
() login.html , RouterOS web . .
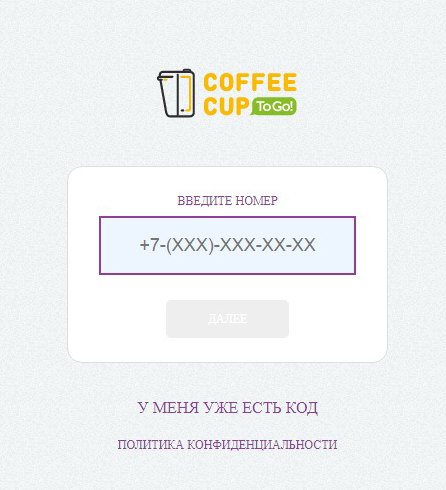
alogin.html , : ( , ). , . , . - , 16 RouterOS Hotspot. , , USB flash, ( ) USB MikroTik. alogin.html 500 . Hotspot , backend.
. MySQL, Hotspot, . backend PHP, . VPN ( -). .
, : , , mac , ip , ip , , ( ). registration. ( MikroTik ) coffeepoints ( ). users, : , . status, 1 2 login logout. , , , : cron mysqldump , .
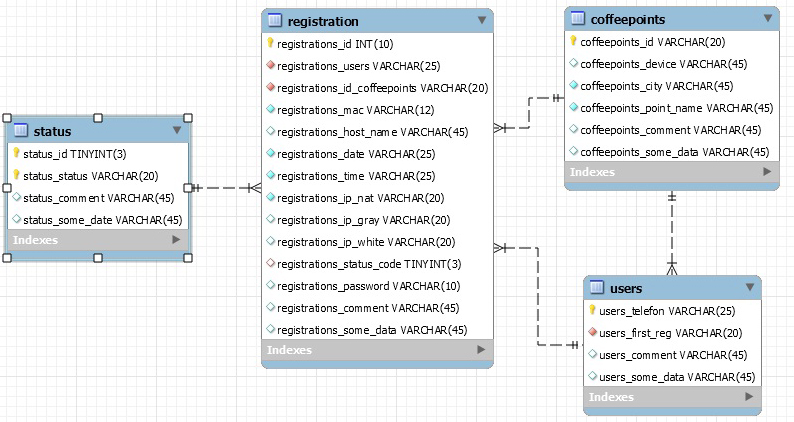
backend. : APIKEY, , . , . , ( users), . status. registrations. APIKEY ( ), .
//
if ( $key_from_get === $api ) {
}
else {
//
$pas1d = random_int (0, 9);
$pas2d = random_int (0, 9);
$pas3d = random_int (0, 9);
$pas4d = random_int (0, 9);
$password = "$pas1d$pas2d$pas3d$pas4d";
echo $password;
}
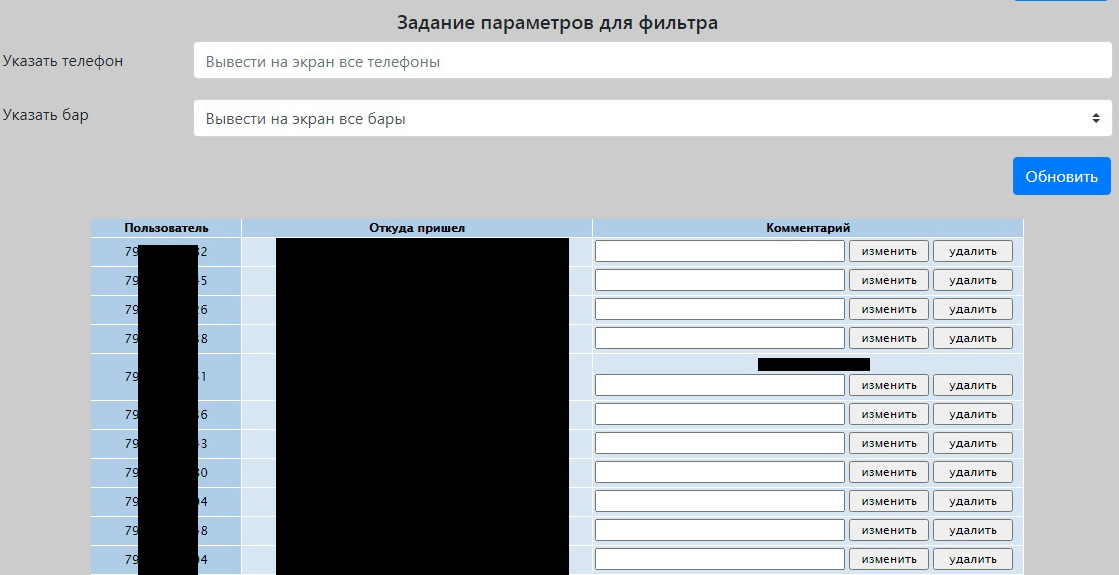
, . , , web ( phpmyadmin adminer), . web , , getbootstrap.com. - frontend. «» , .. registrations .

«» users, «» coffeepoints, «» status, «» . , backend, . , "MS Exel". , . .
VPN. , VPN ( ), OpenVPN, , . : , , . RouterOS, , TCP OpenVPN, . , . , «Safe mode» ( MikroTik, ), firewall - . , , mac , .
結論
最後に、私たちの記事は終わりました。インターネット上で利用可能な開発に基づいて、MikroTik機器のパワー、PHPのパワー、およびMySQLの汎用性を使用して、現在のロシアの法律の枠組み内で動作する、コーヒーカップ会社のバー向けのホットスポットサービスを独自に開始しました。私たちは、さまざまなテクノロジーを実験して扱うことを恐れません。みなさん、2021年おめでとうございます!